Monday, 18 May 2026
Popular News
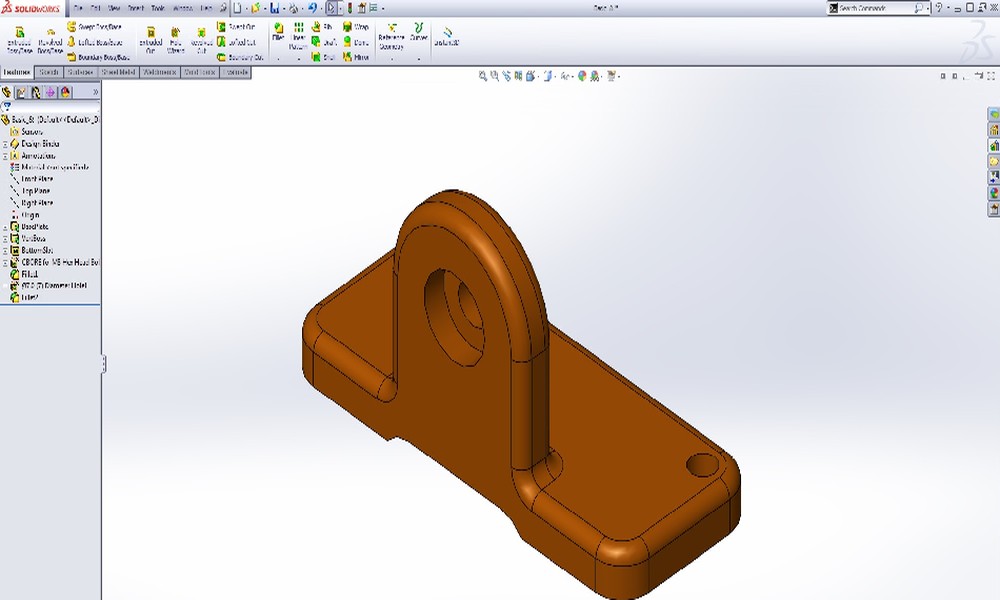
Get Mastercam for SolidWorks at an Unbeatable Price...
- BY Rosalyn R. Cline
- April 23, 2026

How an AI Paper Finder Keeps You Ahead...
- BY Alicia P. Frith
- April 22, 2026
Tech
Get Mastercam for SolidWorks at an Unbeatable Price — Full Version with No Subscription Fees
- BY Rosalyn R. Cline
- April 23, 2026
- 0 Comments
Tech
How an AI Paper Finder Keeps You Ahead With Custom Research Feeds
- BY Alicia P. Frith
- April 22, 2026
- 0 Comments
Tech
How does monitoring software prevent costly compliance violations?
- BY Alicia P. Frith
- April 18, 2026
- 0 Comments
Tech
How does a web design agency structure visual storytelling in modern websites?
- BY Anthony P. Mosher
- March 18, 2026
- 0 Comments
Tech
The Future of Network Threat Detection: Trends to Watch in 2026 and Beyond
- BY Rosalyn R. Cline
- March 16, 2026
- 0 Comments





